What This Guide Gives You
Operational technology has left behind the era of simple perimeter security. In 2026, OT network segmentation is mission-critical for stopping lateral attacks, protecting safety systems, and limiting downtime. This guide lays out what good segmentation actually looks like, how to avoid the most common mistakes, and how to measure progress with clear, practical examples.
Introduction
OT networks run the machinery and infrastructure that keep factories turning, power grids stable, and transportation moving. As these environments have become more connected – to IT systems, cloud services, vendor portals, and remote monitoring – they’ve also become easier to breach. Yet even as risks escalate, many organizations treat industrial network defenses like they did a decade ago: as static and isolated constructs.
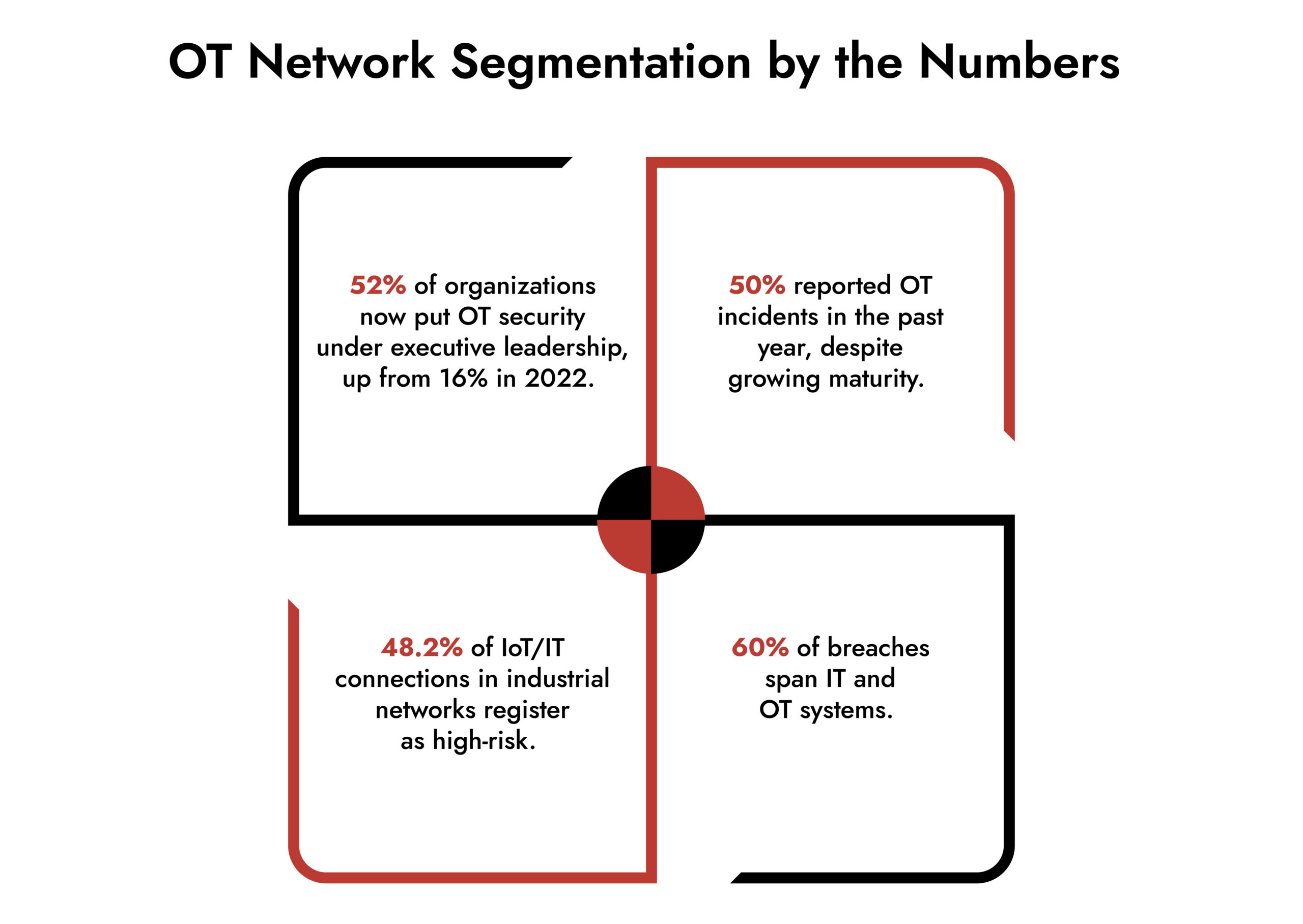
That mindset no longer works. More than half of organizations now elevate OT cybersecurity to the C-suite, recognizing that traditional boundaries no longer protect operational continuity.
A strong OT network segmentation strategy does three things that matter in 2026:
- Limits how far attackers can travel once they’re inside.
- Protects mission-critical systems from cascading outages.
- Enables effective detection and response without disrupting operations.
This blog explains how to achieve that, with concrete examples and current data.
OT Network Segmentation Today – Why It Matters
OT environments no longer operate in isolation. Nearly half of industrial systems are exposed to threats carried in from IT and IoT devices. In a study, 48.2% of network traffic from connected devices was tagged as high-risk, meaning a single compromised sensor or controller could give an attacker a foothold.
At the same time, OT attacks are growing in both frequency and sophistication. Recent analysis shows attackers leveraging lateral movement and living-off-the-land techniques to hide in traffic and bypass simple safeguards.
This isn’t an abstract risk. The manufacturing, energy, and transportation sectors reported that OT incidents disrupted production and safety systems more often than in previous years. Effective OT network segmentation stops these paths before they become crises.
Core Principles of Industrial Network Segmentation
Segmentation isn’t just splitting a network into chunks. It’s about mapping zones to risk and function, then enforcing boundaries that matter under attack conditions.
Design Segmentation Based on Operational Impact
Start with what your systems do, not where they sit on a diagram.
Example: A packaging line and a product tracking system might appear close on a network map. But if a compromise of the packaging controller can halt your entire plant, that controller should live in a separate zone with the tightest controls.
Risk-based segmentation means:
- Classifying systems by business impact.
- Setting controls that match consequences, not convenience.
- Reviewing these classifications regularly as operations evolve.
This makes OT cybersecurity measurable, not theoretical.
Enforce Strong IT-OT Boundaries
When IT and OT merge without controls, attackers move easily from enterprise systems into industrial ones.
Protect this boundary with:
- Dedicated demilitarized zones (DMZs) for data flows.
- Protocol-aware filtering between IT and OT.
- Time-bound, role-based vendor access.
Make sure access rules aren’t all “allow” by default.
Segment by Function First, Asset Type Second
Grouping everything by device type (all Programmable Logic Controllers or PLC here, all sensors there) rarely stop modern attacks. Functional segmentation groups systems by what they control and how their failure impacts the business.
Example: Separate:
- Safety instrumented systems (SIS) from production sequencing controllers.
- Historian servers from real-time control networks.
Function-driven zones reduce the blast radius of malware and help defenders spot anomalies faster.
Upgrade Legacy OT with Compensating Controls
Most critical controllers and field devices were never designed with security features like encryption or patching. You can’t just install an agent and call it secure.
In practice, that means:
- Implement segmentation at the network and conduit level.
- Use protocol proxies and gateways that understand Modbus, EtherNet/IP, OPC UA, and other industrial protocols.
- Restrict communication to exactly what’s needed and nothing more.
This approach guards legacy systems without risking production uptime.
Visibility and Detection – The Other Side of Segmentation
Segmentation alone isn’t enough. Blind enforcement breeds blind spots. Effective OT network security pairs segmentation with continuous monitoring.
That means:
- Capturing and analyzing traffic across zones.
- Looking for deviations that rules don’t catch.
- Correlating OT events with IT logs to understand cross-domain activity.
Without visibility, you can’t prove your network segmentation works.
Real-world example: An energy utility discovered lateral movement not through firewall logs, but by watching anomalous Modbus commands sent from a vendor workstation to its SCADA network – something segmentation alone had not blocked.
Tools that understand industrial protocols (rather than simply IP addresses and ports) make all the difference here.
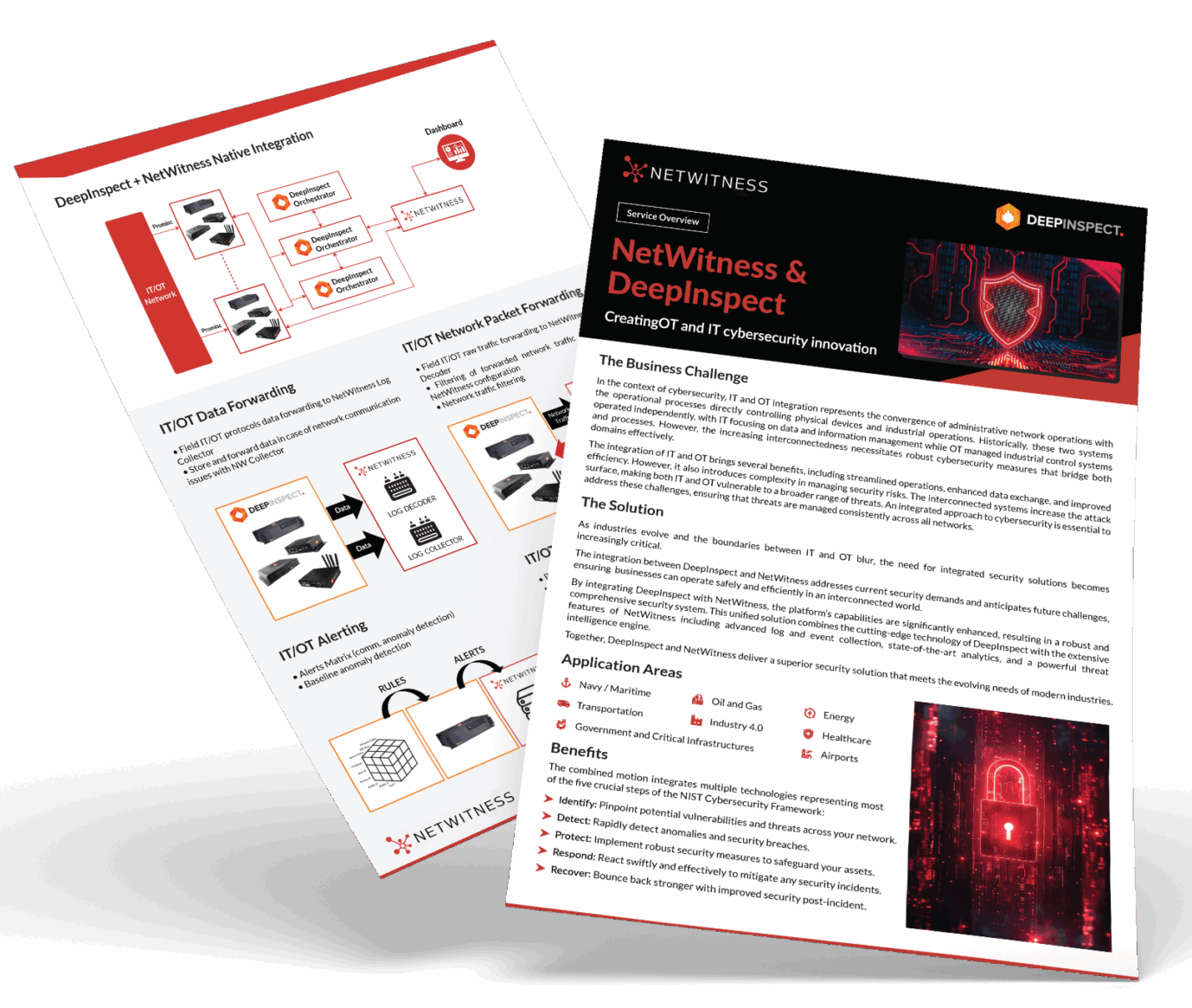
Unify IT and OT Threat Detection with NetWitness® and DeepInspect
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.
Common Mistakes That Weaken Segmentation
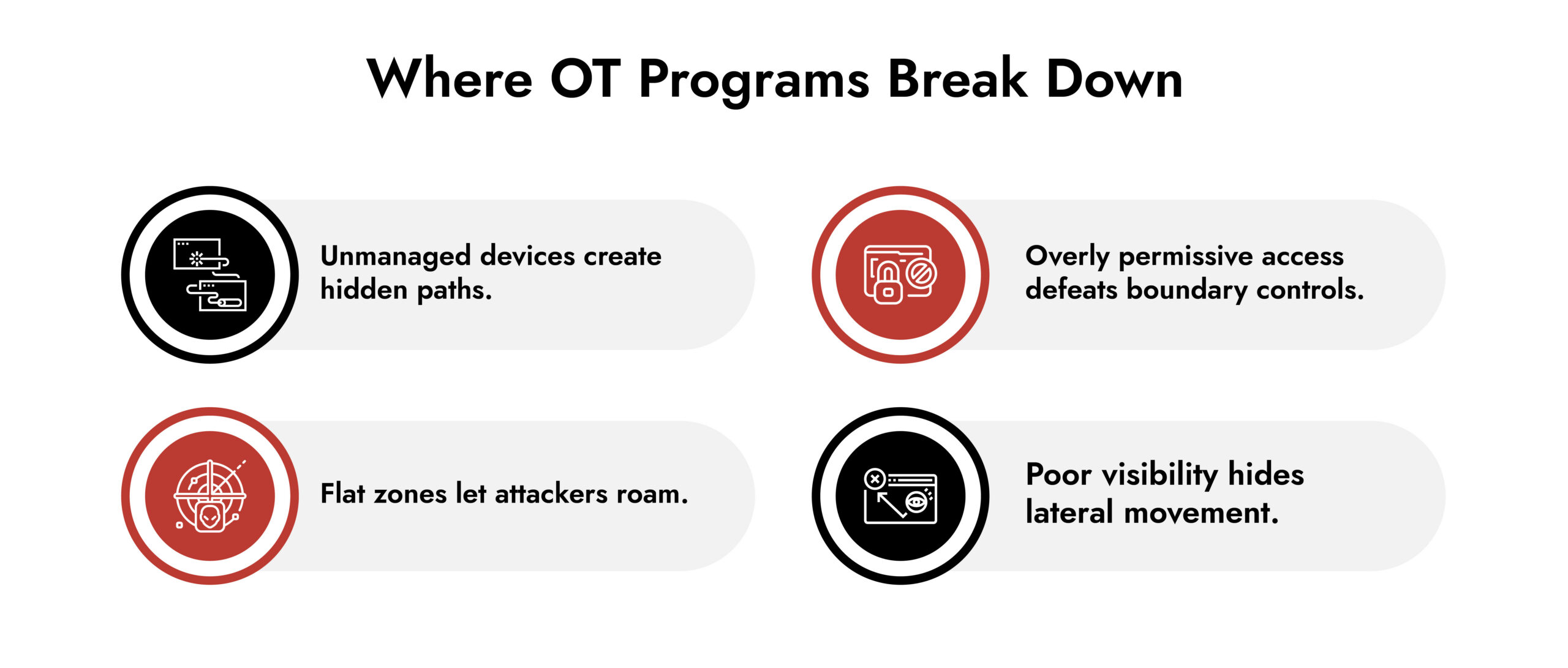
Lack of Asset Inventory
If you don’t know what’s on the network and how it communicates, you can’t protect it. Up to 30% of industrial devices on some networks remain unmanaged or unidentified.
Too Many Manual Rules
Over time, manual add-ons to firewall rules and ACLs become unmanageable. Standardize and automate where you can.
Ignoring Organizational Silos
IT teams focus on data; OT teams focus on uptime. Without deliberate governance, this divide weakens segmentation, enforcement, and response.
How Segmentation Supports OT Threat Detection
Segmentation compartmentalizes risk. Detection tools amplify its value:
- Alerts trigger faster when traffic crosses unexpected boundaries.
- Investigations start with smaller scopes, shortening response time.
- Playbooks can map specific zones to known threat behaviors.
Segmentation becomes measurable when tied to outcomes like reduced dwell time and quicker containment.
How NetWitness Strengthens OT Network Segmentation
OT network segmentation is effective only when teams can monitor, confirm, and apply it consistently. This is how NetWitness integrates into contemporary operational technology security initiatives.
NetWitness facilitates OT network segmentation by delivering comprehensive, protocol-informed visibility across industrial settings without the need for agents on delicate or outdated systems.
Here’s its significance in real-world applications.
Full Visibility Across Segmented OT Zones
Segmentation defines boundaries. NetWitness verifies them.
NetWitness captures and analyzes OT traffic across zones and conduits, including industrial protocols such as Modbus, DNP3, OPC UA, and EtherNet/IP. This allows security teams to confirm that communication paths behave exactly as designed and to detect when systems cross boundaries they should never cross.
Example: If a maintenance workstation in a low-risk zone suddenly initiates control-level commands toward a safety system, NetWitness surfaces that behavior immediately, even if firewall rules technically allow the traffic.
Detecting Lateral Movement Inside OT Networks
Attackers rarely break systems outright. They move quietly.
NetWitness enables OT threat detection by identifying:
- Unauthorized east-west communication between controllers
- Abnormal command sequences within industrial protocols
- Deviations from established process behavior
This visibility turns OT network segmentation into an enforceable control, not just an architectural assumption.
Supporting Legacy Systems Without Disruption
Most OT environments rely on equipment that cannot support endpoint agents or frequent patching.
NetWitness operates passively on the network, making it suitable for:
- Legacy PLCs and RTUs
- Safety instrumented systems
- Continuous process environments where downtime is unacceptable
This approach aligns with real-world OT cybersecurity best practices, where network-level controls must compensate for endpoint limitations.
Aligning Segmentation with Incident Response
When segmentation and detection operate together, response improves.
NetWitness provides session reconstruction and contextual evidence that helps teams understand:
- Which zone was affected
- How the attacker moved
- What systems were touched
That clarity reduces response time and supports operational decision-making when minutes matter.
In short, NetWitness doesn’t replace OT network segmentation. It makes it provable, observable, and defensible in real industrial environments.
Conclusion
Effective OT network segmentation in 2026 isn’t about neat diagrams or checklists. It’s about building boundaries that reflect real risk, enforcing them with visibility, and adjusting as systems and threats evolve.
This is about protecting operations and safety while enabling innovation, not blocking it.
Review your segmentation strategy. Ask whether it limits lateral movement, aligns with operational impact, and feeds detection systems. If it falls short, it’s time to rethink it.
If you want help mapping segmentation to real industrial risk – from PLCs to remote access – reach out. Resilience starts with clarity.
Frequently Asked Questions
1. What is OT network segmentation?
It’s the practice of breaking operational technology environments into secure zones and controlled conduits to restrict access and reduce the impact of attacks.
2. What are the core best practices for OT network segmentation in 2026?
Start with risk-based zones, enforce IT-OT boundaries, segment by function, compensate for legacy devices, and link segmentation with continuous OT threat detection.
3. What are common challenges in implementing OT network segmentation?
Challenges include incomplete asset visibility, legacy devices without security features, too many manual rules, and misalignment between IT and OT teams.
4. How does OT network segmentation improve security?
It limits lateral movement, protects critical systems, and gives defenders more time to detect and respond to threats.
5. Why must OT segmentation be paired with visibility?
Segmentation without visibility leaves blind spots. Monitoring across zones reveals anomalies that static rules can’t detect.
6. How does segmentation fit into broader OT cybersecurity best practices?
Segmentation complements access control, identity management, threat detection, and incident response as part of a comprehensive operational technology security strategy.
FIN13: Inside a Fintech Cyber Attack
FIN13 is one of today’s most disruptive threat groups targeting fintech organizations with precision and persistence. This whitepaper breaks down their full attack chain—from reconnaissance and credential theft to lateral movement, data exfiltration, and evasion techniques. Gain insights into their TTPs, discover detection opportunities across the kill chain, and learn how NetWitness empowers faster response and mitigation.